Reports about Anthropic’s Mythos capabilities have recently dominated cybersecurity headlines. The company claims that the tool can outperform humans in cybersecurity tasks, autonomously discovering thousands of software vulnerabilities—even dormant bugs in decade-old code.
What Is Anthropic’s Mythos?
Mythos is one of Anthropic’s latest AI models, developed as part of the broader Claude ecosystem. Introduced in early April as the “Mythos Preview,” the model has shown remarkable proficiency in cybersecurity tasks. Researchers testing Mythos reported that it identified vulnerabilities previously undiscovered by human experts—including a 27-year-old OpenBSD bug and a 16-year-old FFMPEG vulnerability.
This demonstrates AI’s growing ability not just to write or review code, but to autonomously find weaknesses in it, effectively performing the work of highly skilled security analysts at machine speed.
A Paradigm Shift in Cybersecurity
While Mythos’ capabilities are impressive, they are not entirely unexpected. As AI models become increasingly proficient in coding and reasoning, it is a natural extension that they can uncover vulnerabilities in insecure software. Research shows that many vulnerability-discovery techniques used by frontier models can already be replicated using low-cost, open-weight AI models. In other words, advanced AI capabilities are becoming accessible, not rare. This represents a double-edged sword:
- Defensive side: AI can accelerate vulnerability discovery and patching, helping enterprises secure systems faster than ever before.
- Offensive side: Threat actors can leverage AI to find and exploit vulnerabilities before or immediately after disclosure.
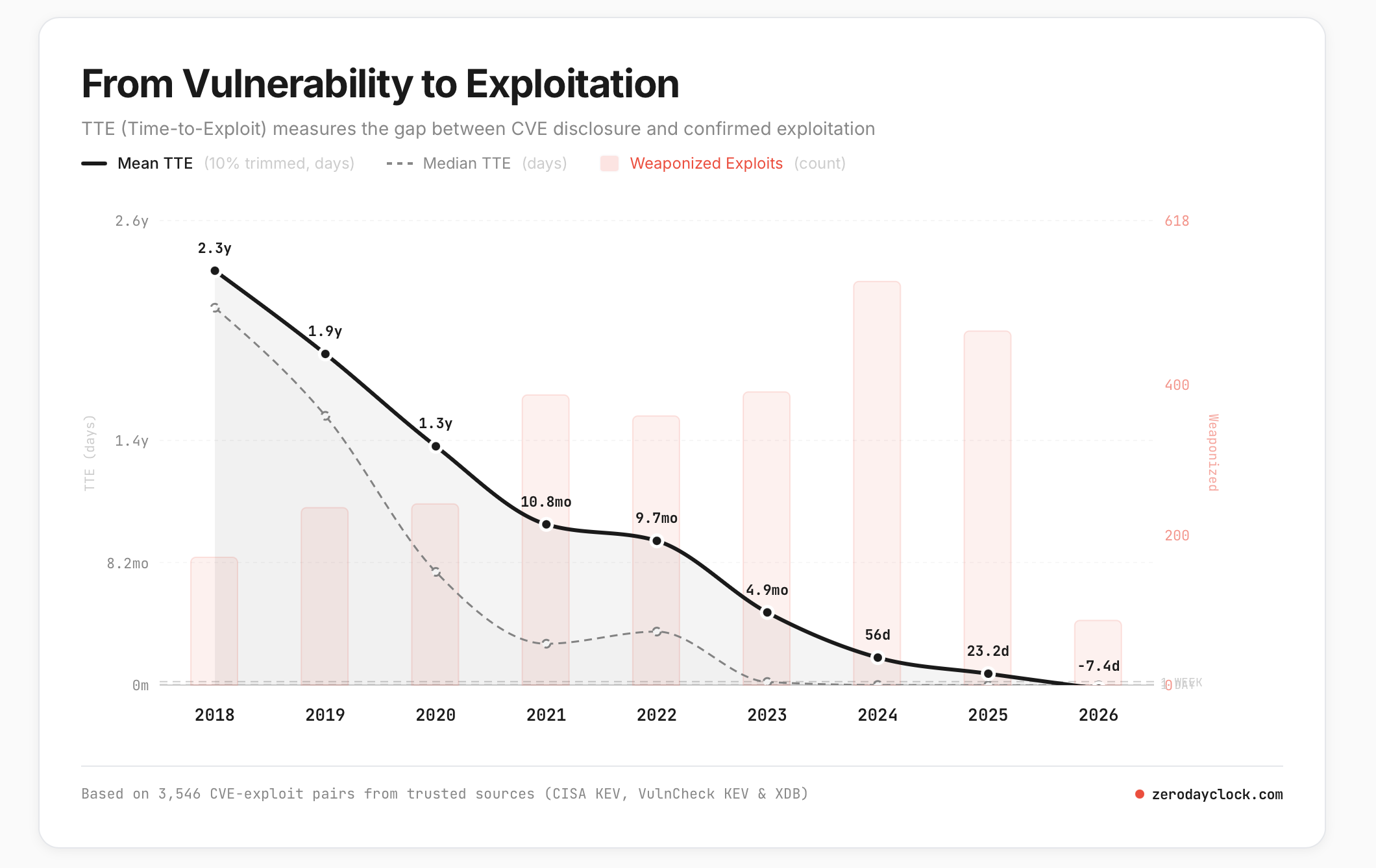
Consider the Time-to-Exploit (TTE) metric from CVE publication to real-world exploits: According to zerodayclock.com, TTE has dropped from an average of 2.3 years in 2018 to around 10 hours in early 2026, (see the Chart above) with projections suggesting it could reach just 1 hour by the end of 2026. Traditional daily or weekly patch management schedules are now insufficient.
Emerging Threats
Beyond accelerating CVE-based attacks, AI introduces a new class of proactive threats: AI-driven zero-day discovery. With falling AI costs and increasing capabilities, threat actors may identify vulnerabilities and develop exploits before software vendors even become aware of them.
Cyber Strategies for the AI Era
So, what can defenders do in this new cybersecurity landscape?
- Maintain Strong Baseline Security Controls Fundamental cybersecurity principles still apply: secure by design, layered defense-in-depth architectures, Zero Trust everywhere, strong identity and access management, and an assume-breach mindset. Cyber resilience solutions must be deployed according to organisational risk.
- Minimise Attack Surfaces
Every internet-facing asset is a potential entry point. Ask yourself about all your internet-facing workloads, are they absolutely necessary to be internet-facing? If the answer is no or maybe, then make them unreachable from the internet directly. If the answer is yes, apply strong network and application firewalls, deploy network segmentation architectures. - Hold Software Makers Accountable
For too long, software makers have prioritised features over security. So there is the famous “Patch Tuesday” for instance. As users, we are at the mercy of software makers providing us with secure software. We must now demand secure software and shift accountability back to makers. - Strengthen Patching Practices
Scheduled patching is obsolete. Organisations must adopt near-real-time patching where possible, leveraging hot-patching capabilities to reduce exposure windows. - Test Incident Response Regularly
An assume-breach mindset demands actionable incident response plans. These plans should be tested frequently and integrated with disaster recovery strategies to ensure overall cyber resilience. - Leverage AI Defensively
Finally, organisations must fight AI with AI. AI can help:
> Harden software systems
> Automate threat detection and hunting
> Monitor activity at machine speed
By using “good AI” to counter “bad AI,” defenders can regain some strategic advantage.
Conclusion
Anthropic’s Mythos is not just a fascinating technology—it’s a warning. AI is dramatically changing the cybersecurity landscape: shrinking patching windows, accelerating exploit development, and democratising both attack and defence capabilities. Enterprises must evolve from periodic security routines to continuous, AI-enabled defence strategies. The future belongs to those who can act at machine speed.